Default configurations and blind trust in user input remain a fantastic way to get your environment flattened. Whether it is your edge appliances or your internal build pipelines, your infrastructure is actively fighting against you.
🚨 Edge RCE in the Wild
CISA just dumped CVE-2025-53521 into the KEV catalog. If you run F5 BIG-IP load balancers or gateways, you have a confirmed, actively exploited RCE vulnerability sitting right on your perimeter. Threat actors are already executing remote code directly on exposed BIG-IP appliances to compromise networks. Drop whatever sprint work you are supposed to be doing and patch your F5 instances immediately before your edge infrastructure becomes a public playground.
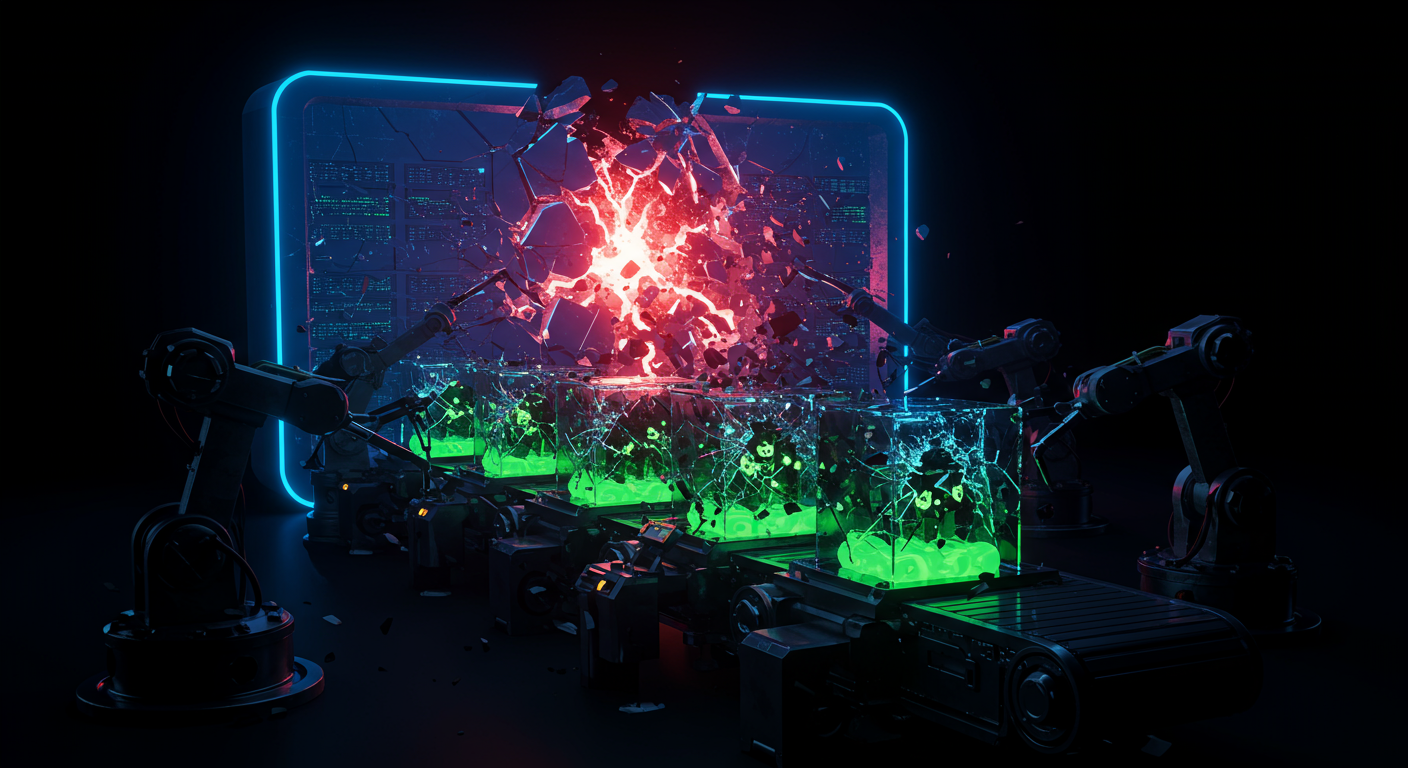
☠️ Global CI Cache Poisoning
If your CI/CD pipelines rely on `act`, Forgejo, or Gitea runners, you could be serving your build environment to anyone who asks. The unauthenticated cache server in `act` listens globally by default. Attackers can guess your cache keys over the network and silently inject malicious artifacts into your workflow. This lets an attacker achieve RCE straight inside your CI containers. Update your runners immediately to enforce token authentication on the cache server and cut off this trivial pipeline backdoor.
🪨 Bricking MinIO Buckets
Flawed server-side encryption metadata handling allows minimally-privileged users to permanently destroy data in MinIO. If any internal user or third-party service holds basic `s3:PutObject` permissions, they can easily spoof `X-Minio-Replication-Server-Side-Encryption-*` headers. The server blindly maps these incoming headers during object creation, writing data with bogus encryption keys and rendering the stored objects permanently unreadable via the S3 API. It turns standard write access into a total data-destruction DoS. Upgrade MinIO now, or configure your ingress proxy to aggressively drop all of those replication headers from incoming requests.