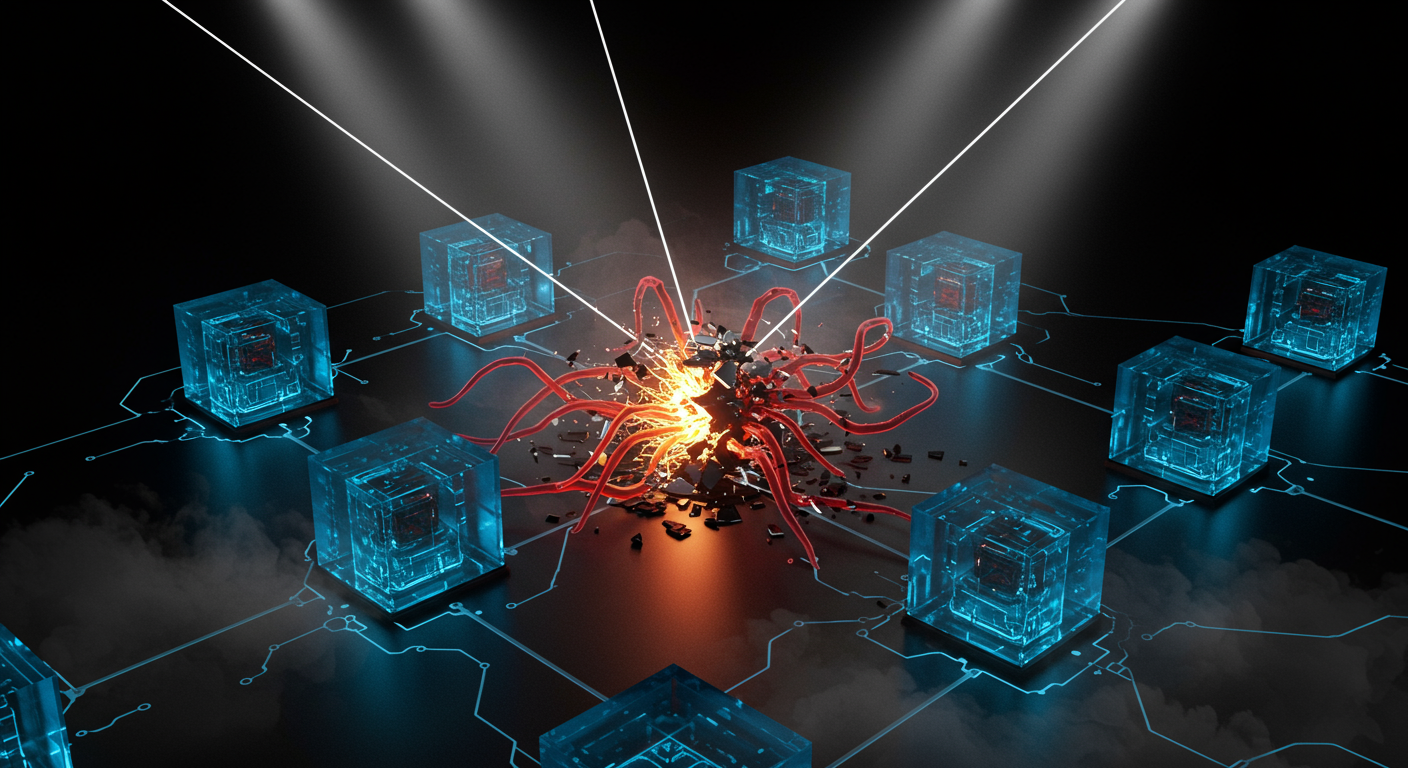
The rush to deploy multi-agent infrastructure has turned basic AI dependencies into primary targets for supply chain compromise and protocol-layer abuse.
🐍 Tainted AI Dependencies
Attackers leveraged a stolen PyPI token to backdoor litellm version 1.82.8. This direct supply chain compromise targets AI builders by embedding a malicious payload that triggers immediately upon installation. Once active, the package silently drops a C2 implant and vacuums up K8s secrets, environment variables, and cloud credentials straight from your active AI workloads.
Guidance:
- Purge `litellm==1.82.8` from all environments and CI/CD pipelines.
- If this specific version was pulled, assume the compromised payload executed.
- Immediately rotate all exposed cloud credentials, environment variables, and K8s secrets.
🤖 Hammering Agent Protocols
Production AI agents are proliferating, and platform teams need an automated way to test structural governance failures instead of just whining about prompt injection. A newly open-sourced testing harness provides 209 protocol-level security tests built specifically to attack multi-agent systems across MCP, A2A, and L402/x402 protocols. The tool actively exploits multi-agent infrastructure to expose vulnerabilities at the protocol layer, validating exactly how fast your governance controls crumble.
Actions:
- Install the newly released test harness and execute it against your multi-agent setups.
- Identify and patch structural protocol weaknesses before attackers can leverage them against your environment.