Supply chain attackers are hiding payload decoders in plain sight using invisible Unicode. Text-based detection won't save you.
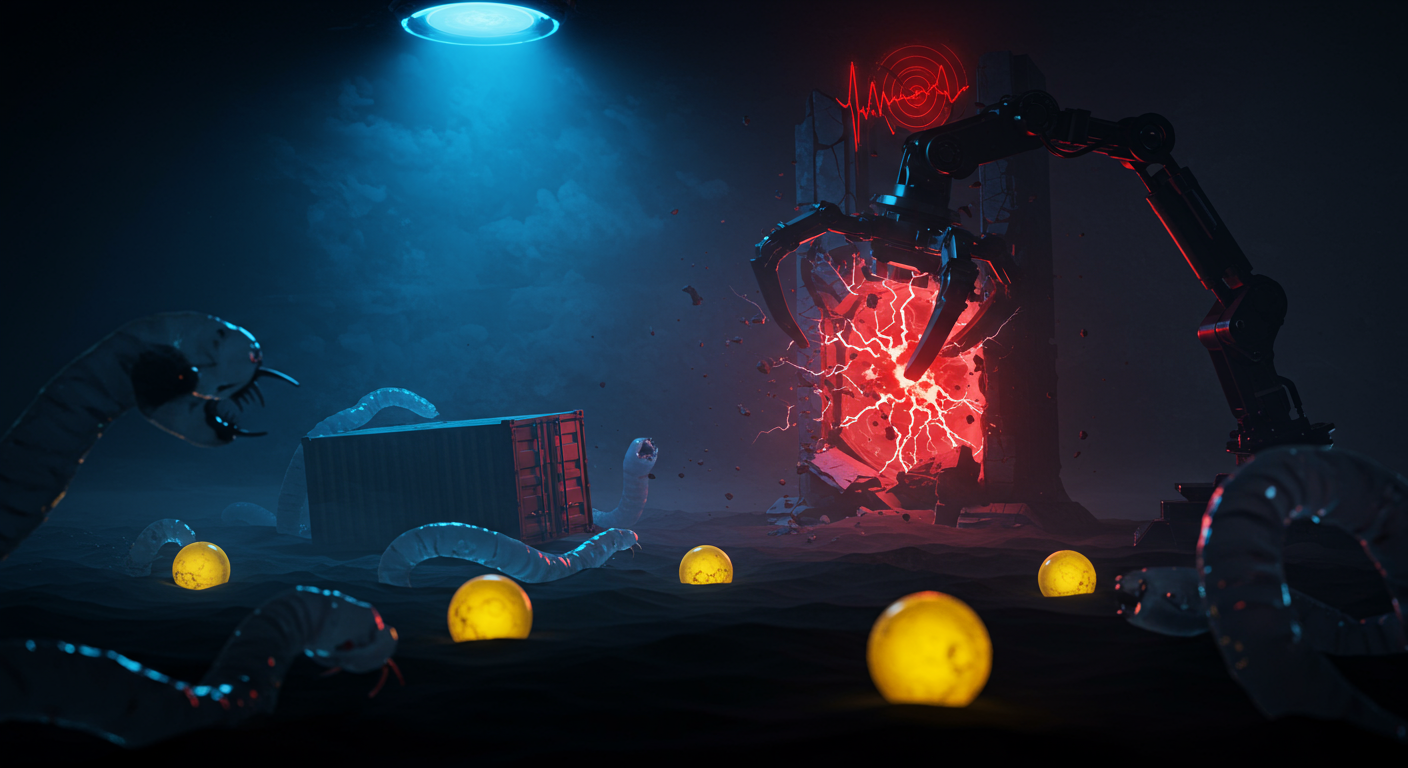
🐛 Hidden Payload Decoders
The GlassWorm campaign has spiked over 400 components since October 2025. The trick? Embedding invisible Unicode into open-source repos. It looks perfectly clean in your IDE, but drops a decoder at runtime to siphon CI/CD secrets and cloud tokens. Standard signature blocking is completely useless against these mutating hidden states. Stop trusting your eyes and drop the Afine heuristic scanner into your CI/CD pipelines before you ship a backdoored component.
🤖 Default-Root AI Containers
Stop deploying AI containers as root and leaving them exposed to the internet. OpenClaw gateways are wide open to CVE-2026-25253 (unauthenticated RCE). A sloppy WebSocket endpoint lacks origin validation, letting anyone execute code directly inside your root-privileged container. Thousands of these are currently sitting exposed with default configs. Strip the root privileges and patch to version 2026.2.23 immediately to close the front door.
🚪 Exposed NetScaler Perimeters
Citrix just dropped critical fixes for CVE-2026-3055 and CVE-2026-4368, hitting NetScaler ADC and Gateway appliances. Since these sit directly on your perimeter, they’re the perfect beachhead for attackers pivoting into your hybrid cloud. Expect mass scanning to start any second. Find your exposed boxes and apply the patches before the inevitable exploit scripts start flying.