Passing the `silent=True` flag in ONNX Hub bypasses trust verification and exposes ML pipelines to unauthenticated models, while standard cloud environments remain full of overly permissive IAM trusts waiting to be enumerated.
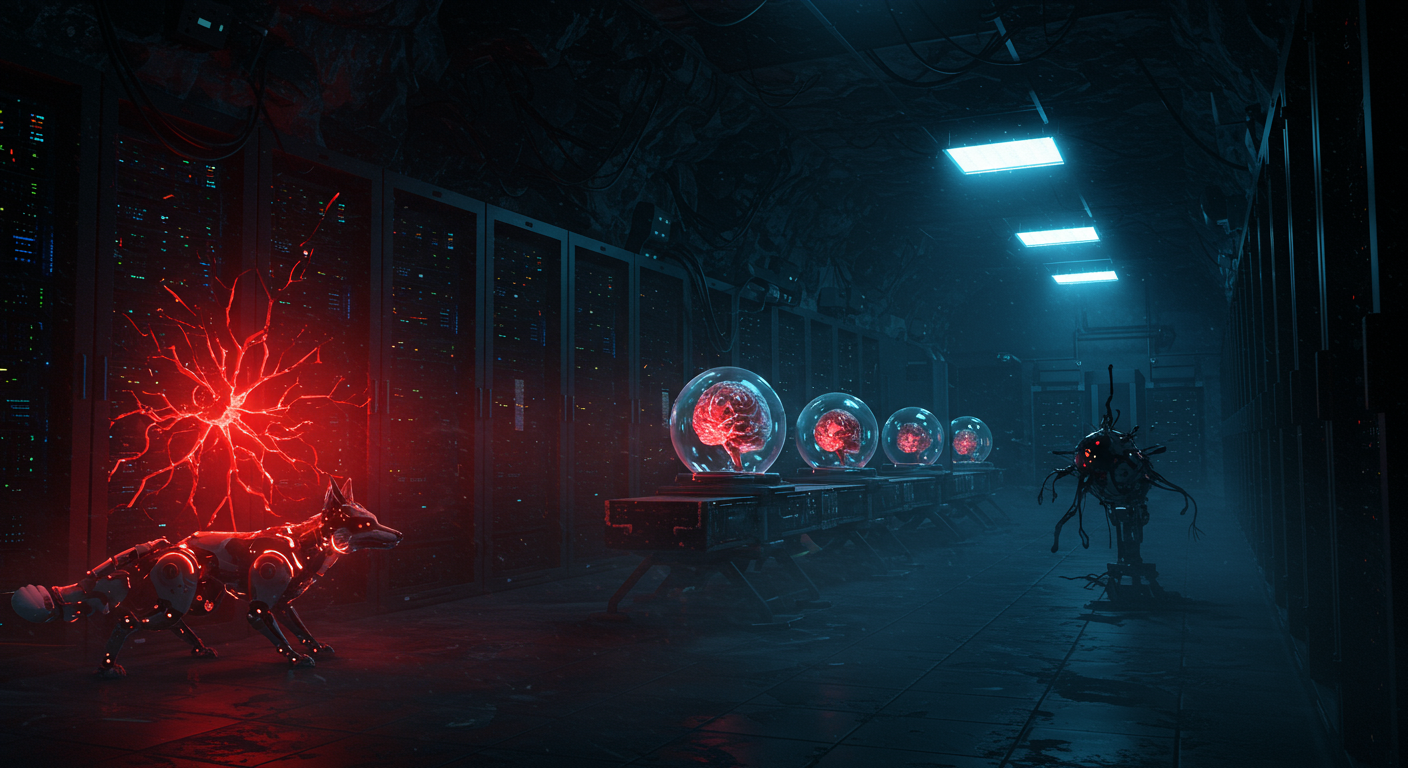
🤫 Silent ML Compromise
When loading models via ONNX Hub, using the `silent=True` parameter completely bypasses trust verification, exposing your infrastructure to an unpatched 9.1 CVSS zero-day (CVE-2026-28500). Passing this flag suppresses the only remaining warning about fetching payloads from untrusted sources.
The underlying trust model is fundamentally broken: the integrity checks against manifests validate the fetched model using a manifest hosted in the exact same repository. An attacker can simply poison the repository with a malicious model and an updated manifest. If your pipeline uses this flag to keep logs clean, it will swallow the malicious payload and execute it without throwing a single error.
- The Fix: There is no patch available. Drop `silent=True` from your ONNX Hub scripts immediately. Force your CI/CD pipelines to break loudly on untrusted sources rather than failing silently.
🦊 Infrastructure Enumeration
Threat actors constantly scrape cloud environments to extract leaked secrets and abuse overly permissive IAM trust policies to escalate privileges and pivot laterally. BishopFox's CloudFox is an open-source penetration testing tool that automates the discovery of these severe misconfigurations.
The tool technically enumerates your attack paths by querying for exposed endpoints and extracting the actual IAM trust relationships mapped across your accounts. It provides a concrete way to identify privilege escalation routes and garbage IAM configurations that leave your infrastructure vulnerable.
- The Fix: Clone CloudFox and run it against your cloud accounts. Find and lock down exposed endpoints and over-permissioned IAM roles before automated external reconnaissance exploits them for you.