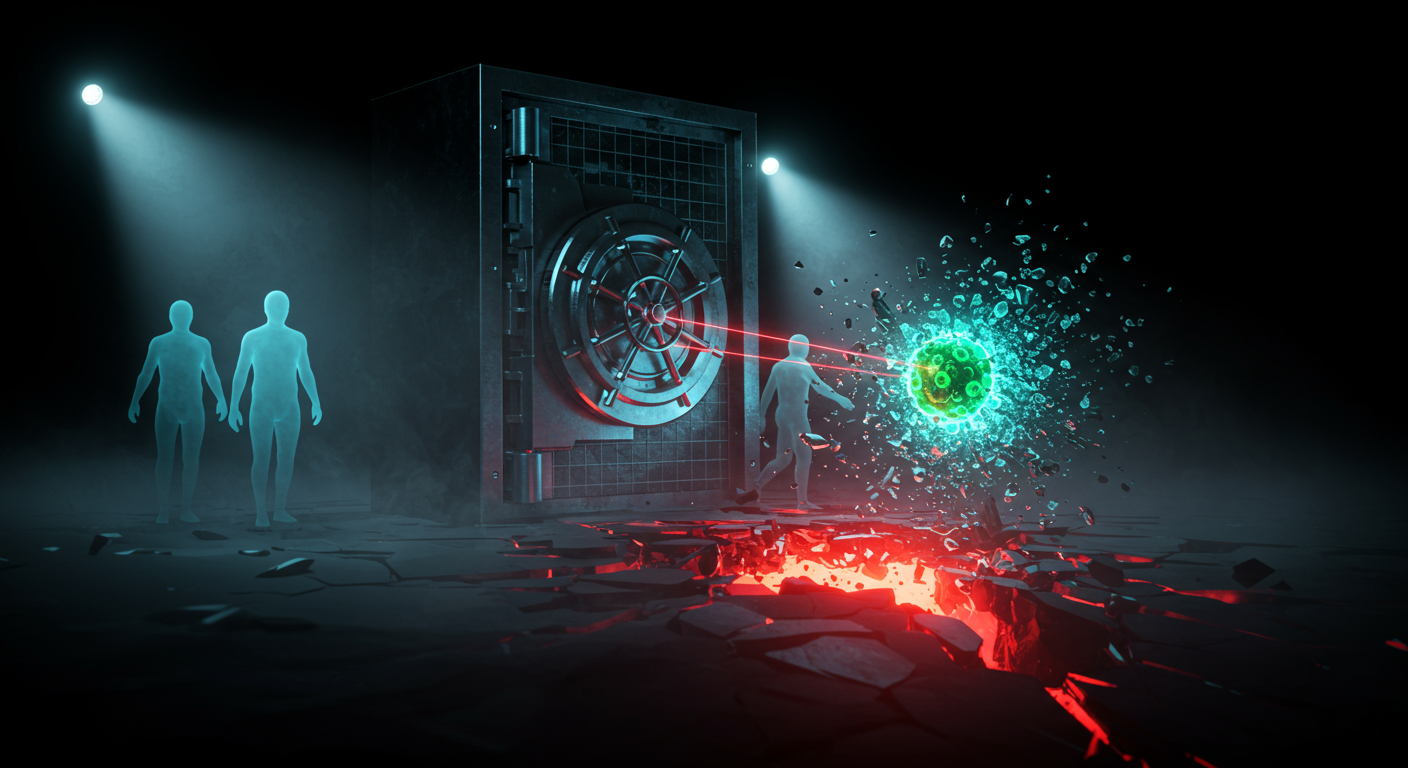
Identity boundaries are dissolving and CLI tools are deciding security prompts are optional.
🪪 Identity Perimeter Shells
Oracle dropped an emergency patch for a critical 9.8 CVSS flaw in Identity Manager. If this appliance touches the internet, unauthenticated remote attackers can execute arbitrary code and own your identity perimeter. It's a tier-zero asset. Apply the patch before ransomware operators turn your identity bridge into a toll road.
👻 Ghost Tokens in Entra
Attackers are manipulating Entra ID auth flows to extract valid tokens while completely bypassing native sign-in logs—for the third and fourth time. If you rely strictly on default telemetry, your SOC is legally blind. Run the exact KQL queries from TrustedSec to hunt for this unlogged token theft before it hunts you.
🚦 Traefik's mTLS Bypass
Using Traefik as an ingress proxy? Fragmented TLS ClientHello packets break its SNI pre-sniffer, causing it to fail open. Instead of dropping the malformed connection, it silently falls back to a permissive state and strips mTLS enforcement. Attackers bypass client certificate validation effortlessly. Upgrade Traefik immediately.
🤖 Workspace Trust Bypass
Anthropic’s Claude Code CLI features a fatal load-order bug (CVE-2026-33068): it processes malicious repo settings before asking the user for workspace trust. If a dev clones a poisoned repo, the CLI instantly elevates permissions and skips the prompt. The machine is compromised before they can even click "deny." Enforce version 2.1.53 across all workstations before your devs own themselves.