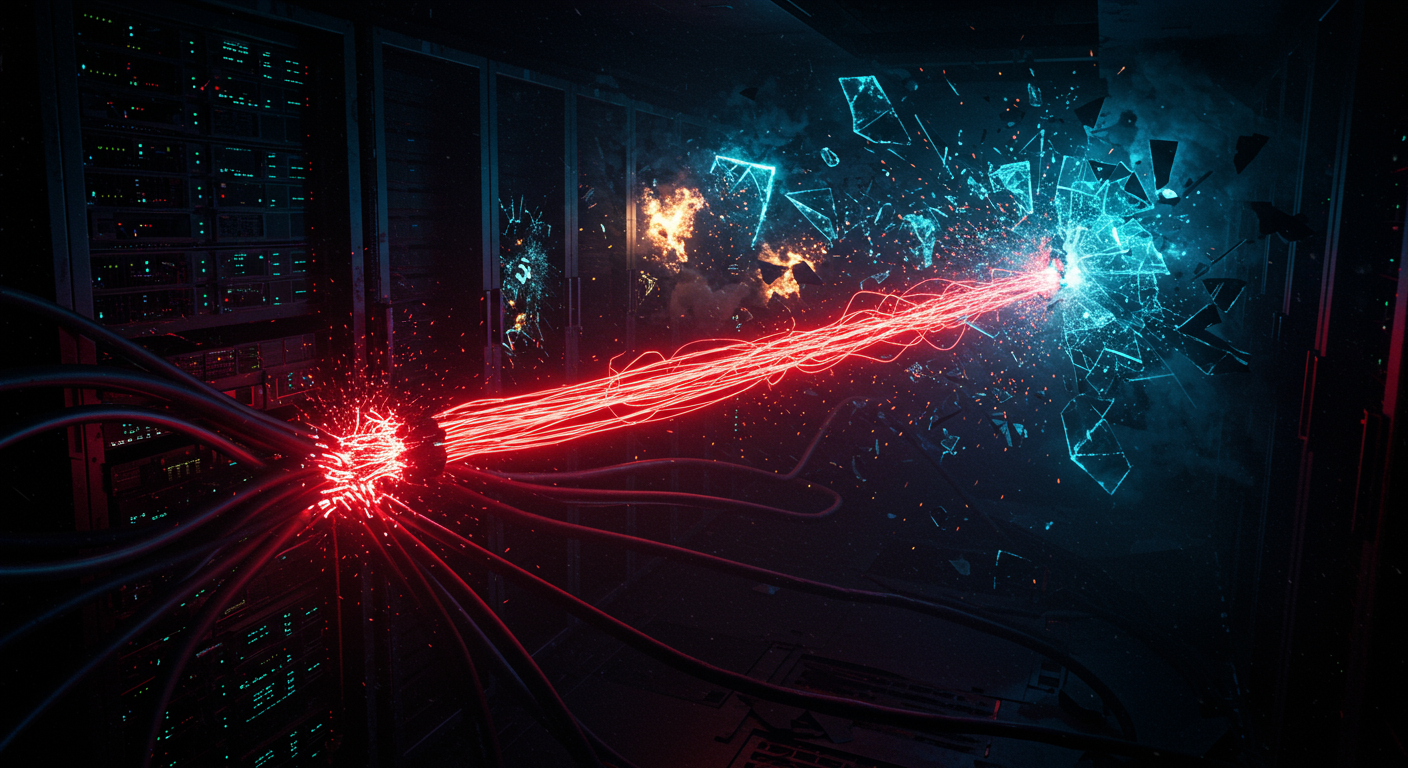
Nothing like watching an enterprise burn because someone forgot MFA for their fleet managers.
🔥 The Single Sign-Out Lie
Killed a compromised Entra ID session? The attacker is likely still camping out in AWS STS and Salesforce. IdP revocation only stops new tokens; downstream federated apps just ride out their existing TTLs. Relying purely on Entra to sever access leaves you completely exposed.
- Action: Build playbooks to manually nuke downstream active sessions alongside your IdP kill-switch. Read the reality check.
🧽 80k Device Wipe
The massive Stryker wipe didn't need zero-days. Attackers scraped stale Intune credentials from infostealer logs and walked right in. Zero MFA turned basic credential theft into a catastrophic wipe of 80,000 endpoints. Cloud MDMs are loaded weapons pointed at your entire fleet. Enforce FIDO2 on all admin accounts. Forensics.
💥 Postgres Panics
Go backends hitting untrusted Postgres URIs have an unpatched zero-click DoS. The `pgproto3` parser completely misses a bounds check on negative lengths. Malicious servers return crafted rows, triggering an out-of-bounds read that instantly panics the Go runtime. Block untrusted URIs and track patches.
🚪 Auth Bypass
Running Heimdall with Envoy gRPC? Relying on deny-lists? Attackers just append a query string to their target URL. Heimdall mangles the Go path encoding, misses the regex, and drops them right into your protected app. Ditch default-allow policies and patch now.
💉 SQLi in JSON Paths
Kysely's compiler for MySQL/SQLite forgets to escape single quotes in `.key()` functions. Pass unsanitized input here, and attackers break the JSON context to run arbitrary SQL. Upgrade to `v0.28.12` to stop trivial UNION-based exfiltration. PoC.